Fog ransomware attack on Asian org used Syteca tracking tool
A Fog ransomware attack took place in May 2025 on a financial institution in Asia, through a legitimate employee-monitoring tool, Syteca, alongside hacking tools such as GC2, as reported by The Record.
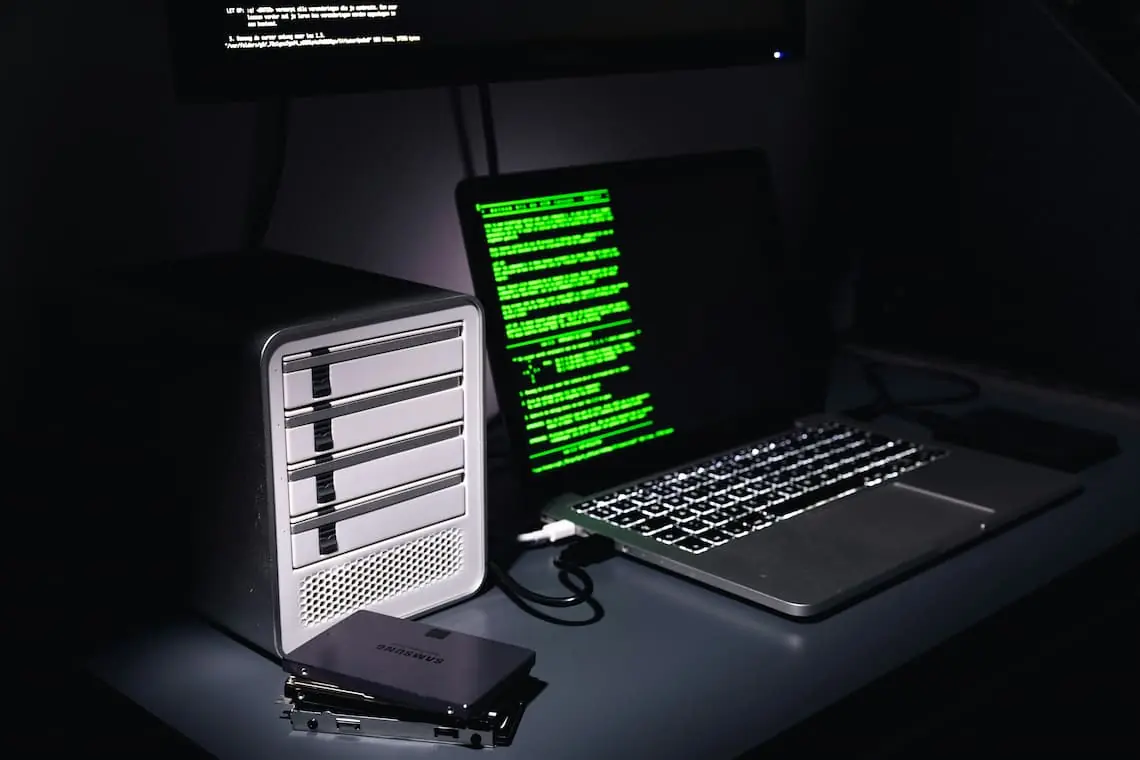
Fog ransomware is a relatively new type of malicious software that exploits vulnerabilities in computer systems to gain access to a network. Once inside, it spreads quickly and encrypts files across the environment, locking victims out of their data.
The attackers ingiltered the institution’s network through Syetca and remained inside the network for about two weeks before launching the ransomware.
Although Syteca is believed to have been used for espionage or data theft, its exact role remains unclear, according to researchers. The attackers later made efforts to cover their tracks by deleting the Syteca executable and configuration files from the network.
The ransomware attack compromised multiple systems, including two Microsoft Exchange servers.
Despite these servers often being targeted by ransomware groups because of long-standing vulnerabilities, it has not been confirmed that they were the initial entry point in this case.
Security experts say such use of commercial surveillance software in ransomware incidents is rare and points to attackers expanding their methods.
Why This Matters for Cyber Defenders
Experts warn that cybercriminals are increasingly using legitimate commercial software in their attacks as it helps them bypass security alerts.
By blending in with approved tools, they can focus on stealing credentials and tricking users through social engineering, rather than creating custom malware, an approach that is especially effective in environments with weak application controls.
The Toolset Deployed
The tool in question, Syteca, was delivered using the Stowaway proxy tool (an open-source proxy tool) and deployed alongside other open-source hacking tools such as GC2 (for running commands and stealing files through Google Drive or SharePoint) and Adaptix C2 Agent Beacon (a penetration testing framework similar to Cobalt Strike).
Background on Fog Ransomware
Fog ransomware emerged in May 2024, initially targeting educational institutions in the US, including an attack on the University of Oklahoma.
Some incidents also involved phishing emails and ransom notes referencing Elon Musk to provoke reactions from victims. A “decrypt for free” option was also offered if victims agreed to spread the ransomware to another computer.
Such occurrences continue to display that attackers, whether those behind Fog or other cybercriminals imitating their methods, are expanding their toolkit with tactics often seen in cyber spying operations carried out by state-backed hackers.
Related Content
Artificial Intelligence to shake up Employee Monitoring
Pros and Cons of Employee Monitoring
Ways to Get Around Screenshot Monitoring